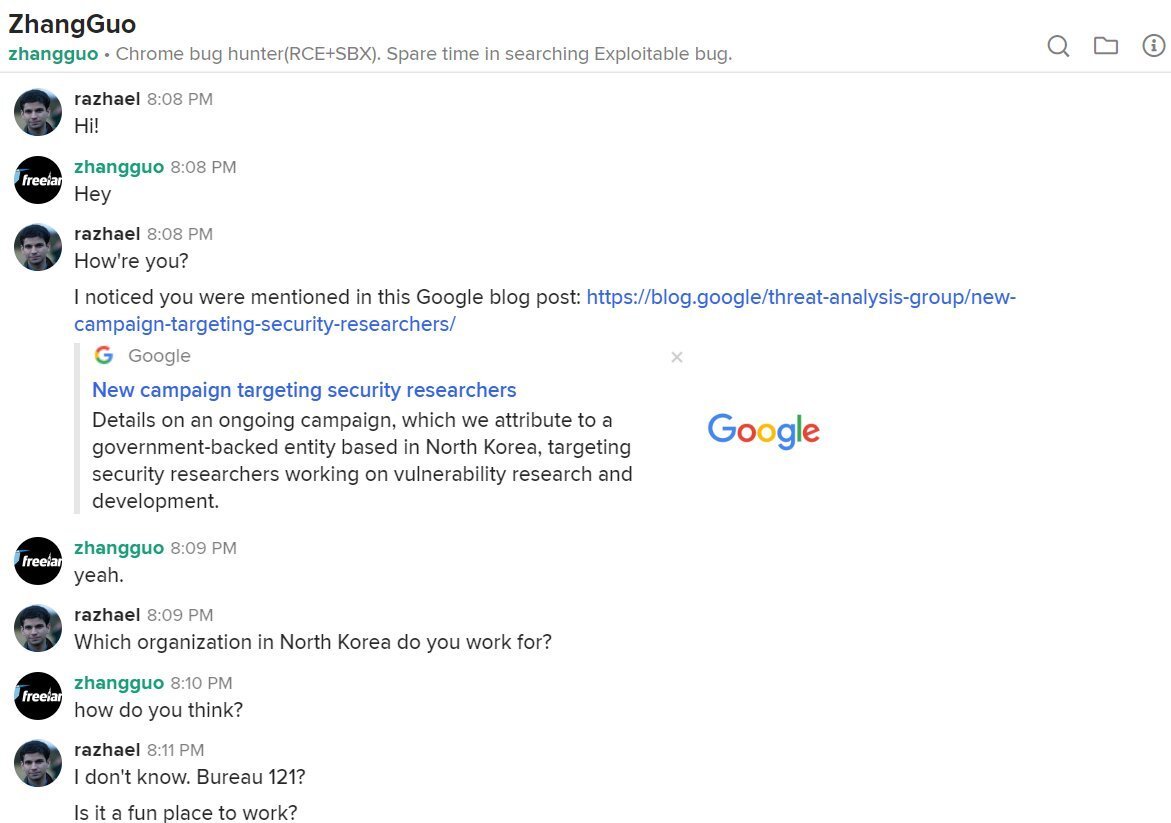
THREAD: Seeing a trend in the drama abt Zhang Guo James Willy et al: "You can't find him, he's in Pyongyang" "DPRK spies" etc, just a general lack of info about N Korea.
I'm from NK Twitter.
Infosec Twitter is shook, but the big context is this s* has been happening for years.
I'm from NK Twitter.
Infosec Twitter is shook, but the big context is this s* has been happening for years.
(This assumes Zhang, Willy, Brown and co. ARE DPRK-linked hackers.)
If they are, they are most likely based in China. You /can/ get internet in the DPRK if you are elite (plebs get their intranet, Kwangmyong), but their telecoms setup is elderly and access is limited by design.
If they are, they are most likely based in China. You /can/ get internet in the DPRK if you are elite (plebs get their intranet, Kwangmyong), but their telecoms setup is elderly and access is limited by design.
Given the open, real-time communication of the hackers on multiple platforms to folks like @razhael, they are likely NOT based in the DPRK. CN, RU, Malaysia etc
Working abroad, there's 1) better internet access 2) can thwart IP-based attribution to DPRK
https://www.nknews.org/2020/08/more-than-6000-hackers-are-working-for-north-korea-worldwide-report-says/
Working abroad, there's 1) better internet access 2) can thwart IP-based attribution to DPRK
https://www.nknews.org/2020/08/more-than-6000-hackers-are-working-for-north-korea-worldwide-report-says/
Good segue-way to their English capability: NK hackers once had horrid English. That led them to c+p fluent Eng emails from compromised inboxes, targeting North Korea policymakers, researchers etc mostly based in the US, NK's sworn enemy.
Case study here: https://www.nknews.org/2020/07/phishing-emails-targeting-north-korea-watchers-grow-increasingly-sophisticated/?t=1611820206519
Case study here: https://www.nknews.org/2020/07/phishing-emails-targeting-north-korea-watchers-grow-increasingly-sophisticated/?t=1611820206519
They leveled up when they began 1) using the identities of real journalists to catfish targets (sound familiar?) & 2) began calling targets on Whatsapp and other platforms w/ good English, possibly by teaming with crime groups
1 https://www.nknews.org/2020/12/hackers-use-fake-media-domains-to-trick-north-korea-researchers/?t=1611820363429
2 https://www.nknews.org/2020/08/north-korean-hackers-called-victims-on-whatsapp-in-bold-attack-on-defense-firms/
1 https://www.nknews.org/2020/12/hackers-use-fake-media-domains-to-trick-north-korea-researchers/?t=1611820363429
2 https://www.nknews.org/2020/08/north-korean-hackers-called-victims-on-whatsapp-in-bold-attack-on-defense-firms/
Also, that's just English. Sophisticated Korean-lang phishing and blunt harassment campaigns against 1) South Korean targets like politicians & 2) NK defectors living in ROK have been going on for decades. They're still at it:
1 https://www.nknews.org/2020/12/north-korean-defector-politician-hit-with-two-mysterious-hacking-attempts/?t=1619655643285
2 https://www.wsj.com/articles/north-korea-harasses-defectors-with-calls-texts-are-you-having-fun-these-days-11597492800
1 https://www.nknews.org/2020/12/north-korean-defector-politician-hit-with-two-mysterious-hacking-attempts/?t=1619655643285
2 https://www.wsj.com/articles/north-korea-harasses-defectors-with-calls-texts-are-you-having-fun-these-days-11597492800
Campaigns became WAY more specific in 2020. 1) "Big-game hunting" w custom ransomware 2) big push to phish defense/aero folks in US, RU, IL, etc via Linkedin, fake job offers 3) rumors that they hacked COVID research centers
1 https://www.nknews.org/2020/07/north-korean-hackers-behind-custom-ransomware-attack-targeting-wealthy-groups/
2 https://www.nknews.org/2020/06/north-korean-hackers-targeted-aerospace-defense-companies-via-linkedin-experts/
1 https://www.nknews.org/2020/07/north-korean-hackers-behind-custom-ransomware-attack-targeting-wealthy-groups/
2 https://www.nknews.org/2020/06/north-korean-hackers-targeted-aerospace-defense-companies-via-linkedin-experts/
NK hackers also began teaming w intl cybercrime orgs, ie Trickbot.
Experts once saw NK hackers as isolated state actors who re-used their own code bits bc they couldn't study other malware due to lack of internet.
They've shed hermit mode and are interacting w targets & collabs
Experts once saw NK hackers as isolated state actors who re-used their own code bits bc they couldn't study other malware due to lack of internet.
They've shed hermit mode and are interacting w targets & collabs
About the spy thing -- They're not TRAINED spies, that's why they do oopsies like respond to DMs from journos
Even tho they're under Reconnaissance General Bureau, NK hackers (AFAIK) funnel thru IT universities onto 'finishing school' in CN/RU. They don't get tradecraft training
Even tho they're under Reconnaissance General Bureau, NK hackers (AFAIK) funnel thru IT universities onto 'finishing school' in CN/RU. They don't get tradecraft training
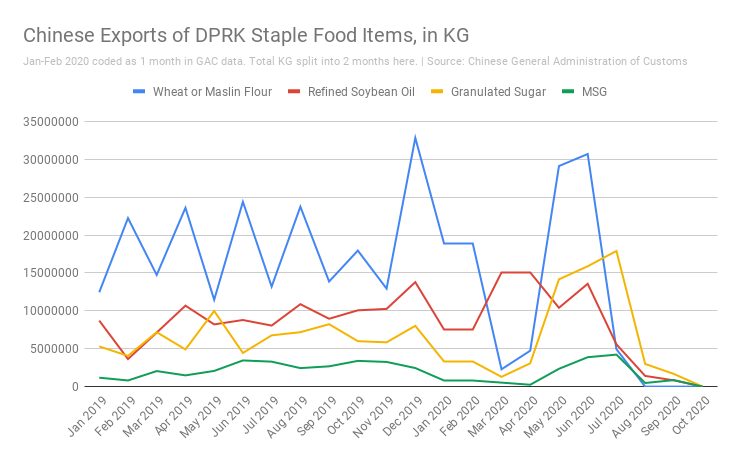
No doubt COVID-19 played a role in the 'leveling up.' The bigger context is the DPRK is HURTING right now, & is taking big risks to get cash and vulns through cyber.
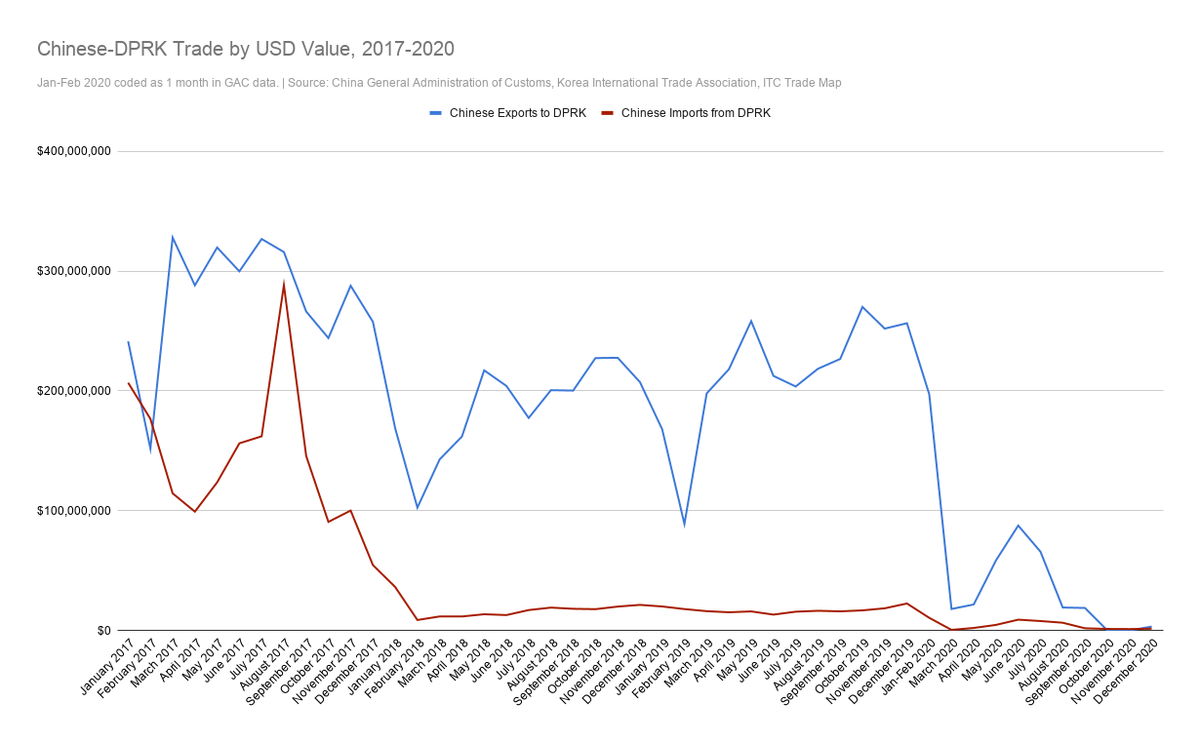
Knowing full-on COVID would end the regime, NK closed its borders in Jan 2020, causing trade to crash 81% YoY(!)
Knowing full-on COVID would end the regime, NK closed its borders in Jan 2020, causing trade to crash 81% YoY(!)
Infosec Twitter is taking the attack personally, but highly specific targeting is just NK's MO now! They were after your vulns and your crypto, but not your nudes.
Zhang+Willy are prob just 1-4 guys sitting in a shitty apt in Liaoning/Jilin under lockdown like all of us.
Zhang+Willy are prob just 1-4 guys sitting in a shitty apt in Liaoning/Jilin under lockdown like all of us.
If you enjoyed this v long thread (thank you for reaching the end) please give the cyber archives at NK News a read~
https://www.nknews.org/tag/cyber/
Also, feel free to Twitter DM me and if you're not a troll I'll get back to you!
https://www.nknews.org/tag/cyber/
Also, feel free to Twitter DM me and if you're not a troll I'll get back to you!
@hacks4pancakes @AlizTheHax0r @alieitan @daveaitel @juanandres_gs @HostileSpectrum @silascutler @_hyp3ri0n @ihackbanme @richinseattle @spoofyroot @pwn_expoit @ShaneHuntley @__winn @TheRealChefG @virustotal

 Read on Twitter
Read on Twitter