Here's a threat on some overpowered technologies to slow down attackers that you can implement _now_.
First, re-implement LAPS ( https://www.microsoft.com/en-us/download/details.aspx?id=46899) at your peril.
1/14
First, re-implement LAPS ( https://www.microsoft.com/en-us/download/details.aspx?id=46899) at your peril.
1/14
Every time I've seen companies roll their own implementation, it's resulted in _any_ compromised workstation being able to retrieve _all_ local Administrator passwords.
Just use LAPS.
2/14
Just use LAPS.
2/14
Lukewarm take: Domain Admins shouldn't be able to log in to regular workstations. If you don't block it via hard policy, it will happen. Constantly. Secure practices don't get year-end bonuses.
https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/plan/security-best-practices/appendix-f--securing-domain-admins-groups-in-active-directory
3/14
https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/plan/security-best-practices/appendix-f--securing-domain-admins-groups-in-active-directory
3/14
Protected Users is the next OP tool. It gets a lot of security wins for all members of that built-in group.
https://docs.microsoft.com/en-us/windows-server/security/credentials-protection-and-management/protected-users-security-group
Start with DA's, one at a time. You'll likely have no issues. Work your way up to all users with any admin rights anywhere.
4/14
https://docs.microsoft.com/en-us/windows-server/security/credentials-protection-and-management/protected-users-security-group
Start with DA's, one at a time. You'll likely have no issues. Work your way up to all users with any admin rights anywhere.
4/14
Credential Guard is _not_ a defense against passing the hash, but it's a powerful defense against attackers gaining password material (Mimikatz-style attacks) from compromised machines directly.
https://docs.microsoft.com/en-us/windows/security/identity-protection/credential-guard/credential-guard
5/14
https://docs.microsoft.com/en-us/windows/security/identity-protection/credential-guard/credential-guard
5/14
More on Credential Guard: It's easy to add to your physical devices (you have a TPM, unless your OEM _really_ screwed you over), but VM's can have a vTPM too, which CredGuard requires.
6/14
6/14
Credential Guard isn't a panacea, but it _is_ a great measure to slow down the Credential Shuffle (as @PyroTek3 named it in section 4: https://adsecurity.org/?p=2362 )
7/14
7/14
What's next? Lock down workstation-to-workstation communication.
If you have strong networking folk, look at Private VLANs ( https://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus5000/sw/configuration/guide/cli/CLIConfigurationGuide/PrivateVLANs.html).
If you have strong AD admins, look at the Windows Firewall via GPO ( https://medium.com/think-stack/preventing-lateral-movement-using-network-access-groups-7e8d539a9029)
8/14
If you have strong networking folk, look at Private VLANs ( https://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus5000/sw/configuration/guide/cli/CLIConfigurationGuide/PrivateVLANs.html).
If you have strong AD admins, look at the Windows Firewall via GPO ( https://medium.com/think-stack/preventing-lateral-movement-using-network-access-groups-7e8d539a9029)
8/14
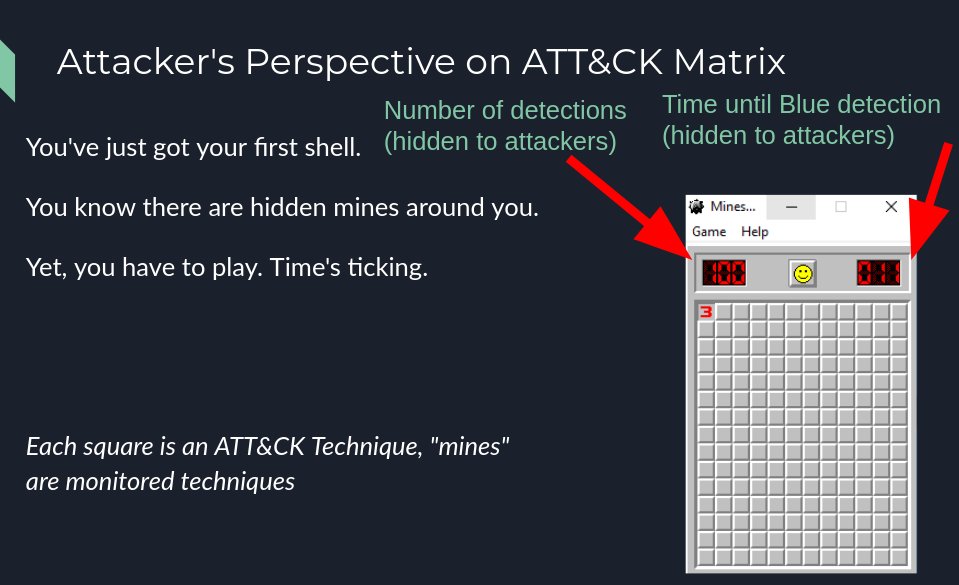
Initial compromise is inevitable. Breaches are not.
To prevent successful breaches, defenders need to detect and respond to attackers before they accomplish their goal. Therefore, defenders have two goals...
9/14
To prevent successful breaches, defenders need to detect and respond to attackers before they accomplish their goal. Therefore, defenders have two goals...
9/14
Defender's Goal #1: Lowering the time to detect and respond to an attacker
Defender's Goal #2: Making it take longer for an attacker to accomplish their goal
10/14
Defender's Goal #2: Making it take longer for an attacker to accomplish their goal
10/14
This thread outlines some great tech for Goal #2. Detective controls are critical, as attackers _will_ eventually succeed unless you detect and respond before they accomplish their goal.
What can you currently detect? https://github.com/redcanaryco/atomic-red-team is a great place to test.
11/14
What can you currently detect? https://github.com/redcanaryco/atomic-red-team is a great place to test.
11/14
Focus your detective control efforts on the TTP's most commonly used by _your_ adversaries.
They need to operate to win. As @brysonbort says, attackers are made of atoms, too, and use the same physics that we do.
From http://bit.ly/findingmalware :
12/14
They need to operate to win. As @brysonbort says, attackers are made of atoms, too, and use the same physics that we do.
From http://bit.ly/findingmalware :
12/14
After the above, here are some initial goals:
Focus on preventive controls until pen tests take longer than a week to go from compromised endpoint to DA.
Focus on detective controls until you can run a tool from src>dst and your SOC can tell you what, where, when, etc.
13/14
Focus on preventive controls until pen tests take longer than a week to go from compromised endpoint to DA.
Focus on detective controls until you can run a tool from src>dst and your SOC can tell you what, where, when, etc.
13/14
The landscape is always changing. Tighten up your security with the above, move to latest supported Windows versions (Windows 10 / Server 2019), and keep nimble.
The ability to change is a pre-req for security.
Thanks for attending my TED talk.
/FIN
The ability to change is a pre-req for security.
Thanks for attending my TED talk.
/FIN

 Read on Twitter
Read on Twitter