A “basic” infosec tool (2FA) is what alerted FireEye to nation state activity.
There are a few things we can learn from this, and not just that my screaming into the void / on conference stages is justified.
A thread (0/8): https://twitter.com/natashabertrand/status/1339380591599497216
There are a few things we can learn from this, and not just that my screaming into the void / on conference stages is justified.
A thread (0/8): https://twitter.com/natashabertrand/status/1339380591599497216
1/8 First, let’s recall that Prospect Theory leads humans to overweight small probabilities (like attackers using 0day chains) and underweight large probabilities (like attackers intercepting 2FA).
Lizard brains gonna lizard brain.
See also: https://swagitda.com/blog/posts/behavioral-models-infosec-prospect-theory/
Lizard brains gonna lizard brain.
See also: https://swagitda.com/blog/posts/behavioral-models-infosec-prospect-theory/
2/8 What’s a counter to lizard brain? Belief prompting, the art of encouraging second / N order thinking — considering your adversaries’ responses to whatever mitigations you implement (then how you respond to their response to your response etc.)
See: https://swagitda.com/blog/posts/choice-architecture-infosec-blue-teams/
See: https://swagitda.com/blog/posts/choice-architecture-infosec-blue-teams/
3/8 We can encourage this via decision trees, where you map out the easiest & least expensive paths attackers can take to get from their initial state to their goal state.
Attackers will 100% be lazy if they can be! So you need to understand & eliminate the lazy options first.
Attackers will 100% be lazy if they can be! So you need to understand & eliminate the lazy options first.
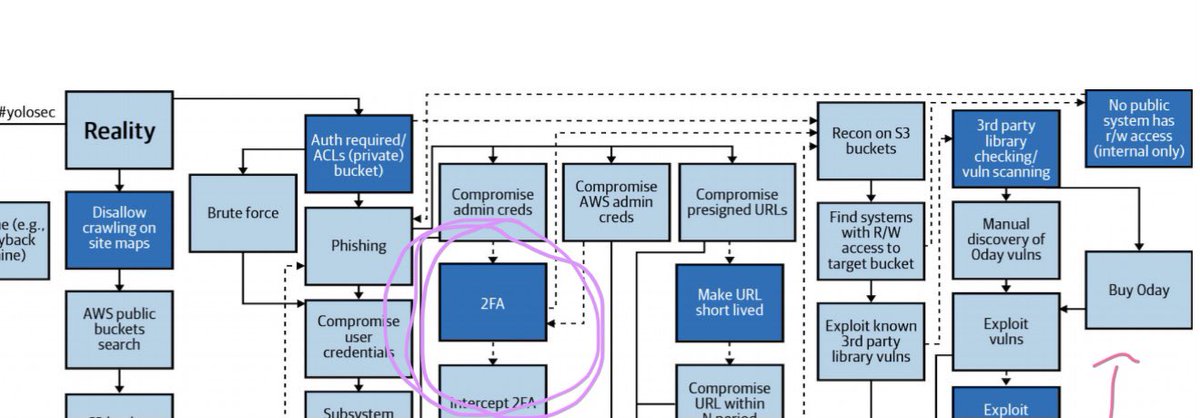
4/8 For instance, you can literally see with decision trees that, if 2FA is implemented, attackers will have to deal with it far earlier than “anti-APT” / anti-0day tools... let alone whatever snakeoil around upstream supply chain security was sold to you.
5/8 As an example, this is a snippet of a decision tree (for an S3 bucket) from my new Security Chaos Eng e-book.
In chicken scratch, I’ve circled 2FA vs. where 0day is. The point: attackers will try to intercept 2FA & only resort to harder shit if they can’t.
Do the basics.
In chicken scratch, I’ve circled 2FA vs. where 0day is. The point: attackers will try to intercept 2FA & only resort to harder shit if they can’t.
Do the basics.
6/8 If you have mitigations — especially detection & quick response — around these easier / cheaper attacker paths, you’re re-balancing ROI.
Right now, attacker ROI outclasses defender ROI. It has for way too long.
2FA in FEye’s breach helped rebalance that ROI.
Right now, attacker ROI outclasses defender ROI. It has for way too long.
2FA in FEye’s breach helped rebalance that ROI.
7/8 “ROI?” you say, “isn’t that an investment thing?”
You’re naive if economics isn’t factoring into your defense, imo, because it’s factored into attacks.
The attack goal isn’t always money, but there are still payoffs and tradeoffs and constraints. Learn & leverage those.
You’re naive if economics isn’t factoring into your defense, imo, because it’s factored into attacks.
The attack goal isn’t always money, but there are still payoffs and tradeoffs and constraints. Learn & leverage those.
8/8 I included a fleshed out decision tree in the SCE e-book along with guidance for how to craft your own (plus more on all the above points).
Learn how to use attacker ROI against them, since they’re already leveraging your lizard brain against you. https://www.verica.io/sce-book/
Learn how to use attacker ROI against them, since they’re already leveraging your lizard brain against you. https://www.verica.io/sce-book/

 Read on Twitter
Read on Twitter