Kraken:
• part of the Hacker’s Toolkit
• runs at startup
• for incident research(!!!)
• logs events but does NOT react
• stores events in local database
(won’t draw attention by
connecting to internet)
“Silent running”? https://twitter.com/intheMatrixxx/status/1327743675443662848
• part of the Hacker’s Toolkit
• runs at startup
• for incident research(!!!)
• logs events but does NOT react
• stores events in local database
(won’t draw attention by
connecting to internet)
“Silent running”? https://twitter.com/intheMatrixxx/status/1327743675443662848
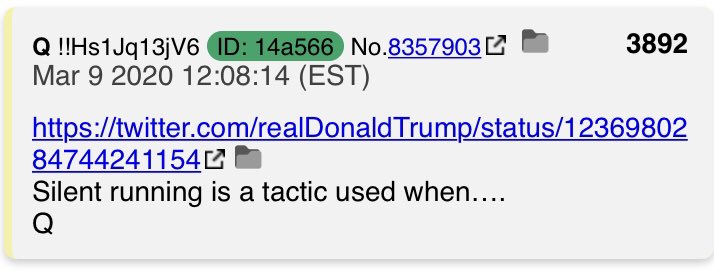
“Silent running is a tactic used when...”
...performing a cyber sting op?
...mapping out the spider web of in/outbound connections to a message board?
...mapping the same for a voting machine?
...doing all of the above while allowing the perps to believe they succeeded?
...performing a cyber sting op?
...mapping out the spider web of in/outbound connections to a message board?
...mapping the same for a voting machine?
...doing all of the above while allowing the perps to believe they succeeded?
Are there any other White Hat examples [events] in which “silent running” appeared to be the mode of operation [allowing the perps to believe they succeeded]?
“Blunt and Direct Time”
“Expect Fireworks”
“Blunt and Direct Time”
“Expect Fireworks”
Was Akayed Ullah’s explosive delivery “silently” swapped out with “fireworks”, but allowed to continue “running”?
Kraken’s Hacker Toolkit site:
https://www.kitploit.com/2020/11/kraken-cross-platform-yara-scanner.html
https://www.kitploit.com/2020/11/kraken-cross-platform-yara-scanner.html

 Read on Twitter
Read on Twitter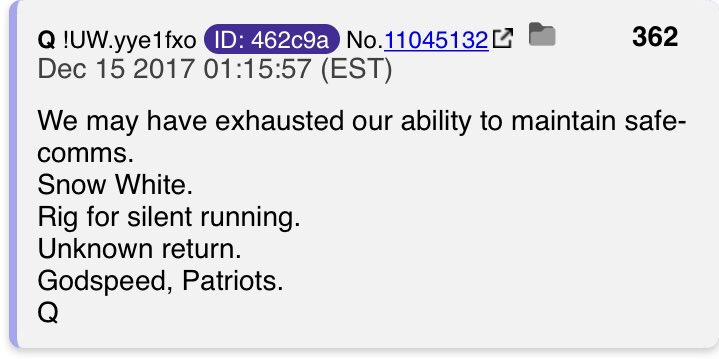
![Are there any other White Hat examples [events] in which “silent running” appeared to be the mode of operation [allowing the perps to believe they succeeded]?“Blunt and Direct Time”“Expect Fireworks” Are there any other White Hat examples [events] in which “silent running” appeared to be the mode of operation [allowing the perps to believe they succeeded]?“Blunt and Direct Time”“Expect Fireworks”](https://pbs.twimg.com/media/Em7RIkOXMAIE0Vp.jpg)
![Are there any other White Hat examples [events] in which “silent running” appeared to be the mode of operation [allowing the perps to believe they succeeded]?“Blunt and Direct Time”“Expect Fireworks” Are there any other White Hat examples [events] in which “silent running” appeared to be the mode of operation [allowing the perps to believe they succeeded]?“Blunt and Direct Time”“Expect Fireworks”](https://pbs.twimg.com/media/Em7RIkNXcAIMobu.jpg)
![Are there any other White Hat examples [events] in which “silent running” appeared to be the mode of operation [allowing the perps to believe they succeeded]?“Blunt and Direct Time”“Expect Fireworks” Are there any other White Hat examples [events] in which “silent running” appeared to be the mode of operation [allowing the perps to believe they succeeded]?“Blunt and Direct Time”“Expect Fireworks”](https://pbs.twimg.com/media/Em7RIkOXcAgGzBN.jpg)




