This is such an awesome writeup, but it's missing one thing - remediation steps
Some AD admins may know how to fix these issues, but it's fair to assume some do not.
I'd also highly recommend using PingCastle by @mysmartlogon as it audits most of this and more.
Thread time! https://twitter.com/InfosecMatter/status/1280958232756981763
Some AD admins may know how to fix these issues, but it's fair to assume some do not.
I'd also highly recommend using PingCastle by @mysmartlogon as it audits most of this and more.
Thread time! https://twitter.com/InfosecMatter/status/1280958232756981763
1) Remove user rights to join devices to AD
Powershell: Set-ADDomain -Identity <Domain> -Replace @{"ms-DS-MachineAccountQuota"="0"} -Verbose
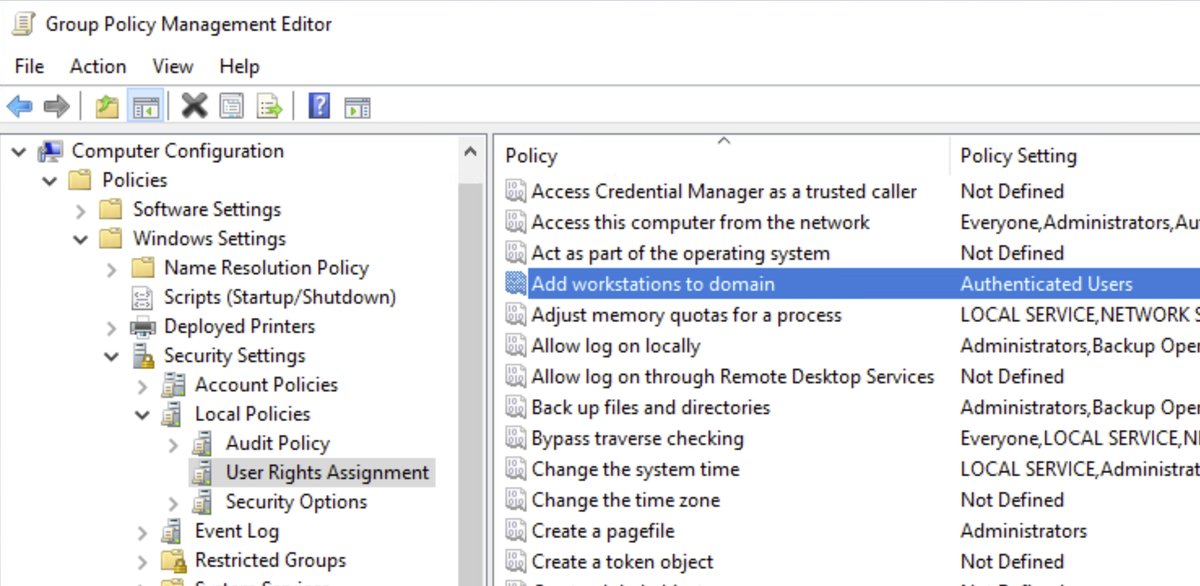
GPO: Modify Default Domain Controller Policy and remove Authenticated Users from the user rights assignment (1st pic)
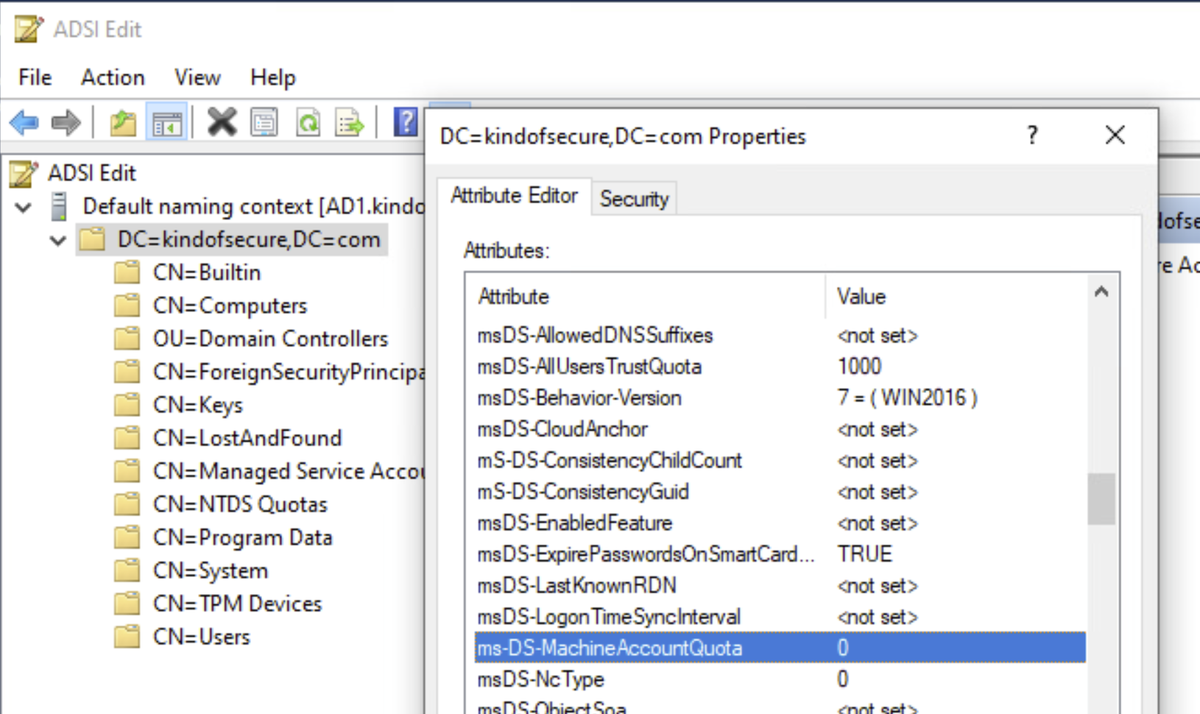
ADSI: (2nd pic)
Powershell: Set-ADDomain -Identity <Domain> -Replace @{"ms-DS-MachineAccountQuota"="0"} -Verbose
GPO: Modify Default Domain Controller Policy and remove Authenticated Users from the user rights assignment (1st pic)
ADSI: (2nd pic)
Instead, consider setting up bind accounts per tier/group/service and delegate to appropriate OU's:
https://www.moderndeployment.com/correct-domain-join-account-permissions/
Also, change binding to create objects in an OU with strict policies:
redircmp "OU=Bind,DC=Domain,DC=Com"
redirusr can be used for users if you want.
https://www.moderndeployment.com/correct-domain-join-account-permissions/
Also, change binding to create objects in an OU with strict policies:
redircmp "OU=Bind,DC=Domain,DC=Com"
redirusr can be used for users if you want.
2) Clear adminCount for non-admin accounts
Run with proper permissions, control click to select ones to clear, click OK, confirm)
Get-ADObject -LDAPFilter "(&(admincount=1)(objectclass=user)" | Out-GridView -PassThru | Set-AdObject -Clear @('admincount') -Confirm -Verbose
Run with proper permissions, control click to select ones to clear, click OK, confirm)
Get-ADObject -LDAPFilter "(&(admincount=1)(objectclass=user)" | Out-GridView -PassThru | Set-AdObject -Clear @('admincount') -Confirm -Verbose
3) Least privilege is simple, not easy
Limit all of these groups:
https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securing-privileged-access-reference-material#tier-0-equivalency
Understand managing privileged identities:
https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securing-privileged-access
Work to empty these groups, use PAWs, get a PAM solution, and leave only honeytokens in there to piss off attackers ;)
Limit all of these groups:
https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securing-privileged-access-reference-material#tier-0-equivalency
Understand managing privileged identities:
https://docs.microsoft.com/en-us/windows-server/identity/securing-privileged-access/securing-privileged-access
Work to empty these groups, use PAWs, get a PAM solution, and leave only honeytokens in there to piss off attackers ;)
4) Service accounts in privileged groups
Look, most apps claiming to need Domain Admin to work are lying to you.
Vendors that do this are lazy and care more about their support time than your security.
Consider using gMSA's with least privilege possible https://docs.microsoft.com/en-us/windows-server/security/group-managed-service-accounts/group-managed-service-accounts-overview
Look, most apps claiming to need Domain Admin to work are lying to you.
Vendors that do this are lazy and care more about their support time than your security.
Consider using gMSA's with least privilege possible https://docs.microsoft.com/en-us/windows-server/security/group-managed-service-accounts/group-managed-service-accounts-overview
5) Extended rights
I'd start with Bloodhound to remove most risky first, then run this script:
https://www.manageengine.com/products/ad-manager/powershell/powershell-get-ad-permissions-report.html
Then:
$securityreport | Select IdentityReference, ActiveDirectoryRights, OrganizationalUnit, IsInherited -Unique | Export-Csv -Path "path" -NoTypeInformation
I'd start with Bloodhound to remove most risky first, then run this script:
https://www.manageengine.com/products/ad-manager/powershell/powershell-get-ad-permissions-report.html
Then:
$securityreport | Select IdentityReference, ActiveDirectoryRights, OrganizationalUnit, IsInherited -Unique | Export-Csv -Path "path" -NoTypeInformation
6) Kerberoasting - he gave great recommendations on this one
Extremely long passwords on services accounts if you can't use gMSA's
Also could evaluate Kerberos Armoring (aka FAST) - just be careful:
https://docs.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2012-R2-and-2012/hh831747(v=ws.11)?redirectedfrom=MSDN#kerberos-armoring-flexible-authentication-secure-tunneling-fast
Also read @PyroTek3 articles: https://adsecurity.org/?p=3458
Extremely long passwords on services accounts if you can't use gMSA's
Also could evaluate Kerberos Armoring (aka FAST) - just be careful:
https://docs.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2012-R2-and-2012/hh831747(v=ws.11)?redirectedfrom=MSDN#kerberos-armoring-flexible-authentication-secure-tunneling-fast
Also read @PyroTek3 articles: https://adsecurity.org/?p=3458
7) Password never expires
Get-ADUser -Filter { passwordNeverExpires -eq "true" }
Convert service accounts over to gMSA's if you can
Many credential vaults from vendors like CyberArk, Thycotic, etc. can rotate strong passwords for you on any AD accounts you need. Evaluate them!
Get-ADUser -Filter { passwordNeverExpires -eq "true" }
Convert service accounts over to gMSA's if you can
Many credential vaults from vendors like CyberArk, Thycotic, etc. can rotate strong passwords for you on any AD accounts you need. Evaluate them!
8) Accounts with no password
Holy crap - give them a password...
9) AD Passwords stored using reversable encryption
Get-ADUser -Filter { userAccountControl -band 128 }
Ask why, and if no one knows, create a new account to test replacing it with at your next opportunity.
Holy crap - give them a password...
9) AD Passwords stored using reversable encryption
Get-ADUser -Filter { userAccountControl -band 128 }
Ask why, and if no one knows, create a new account to test replacing it with at your next opportunity.
10) Storing passwords using LM Hashes
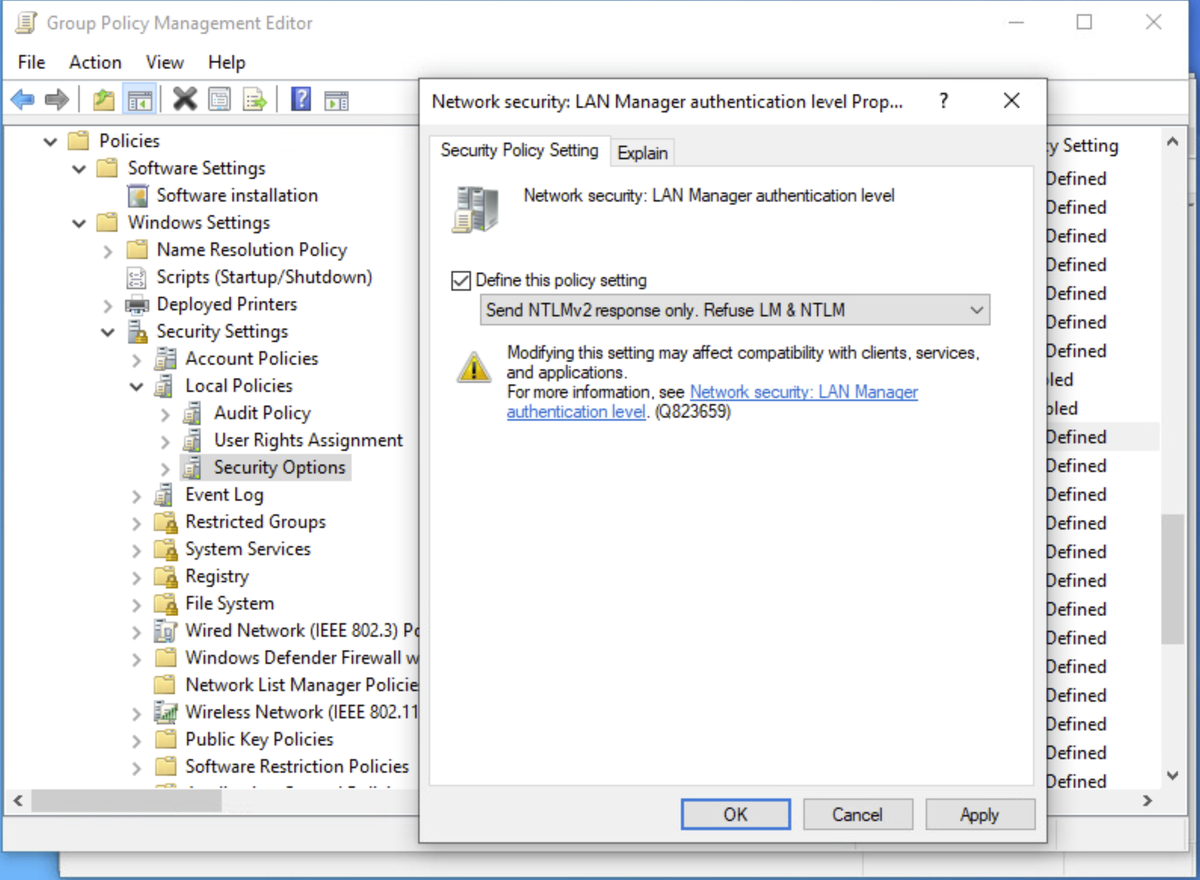
Set GPO to NTLMv2 only, no v1 or LMHash (see pic)
11) Accounts vulnerable to AS-REP roasting
Get-ADuser -filter { DoesNotRequirePreAuth -eq "True" }
Ask why no Kerb preauth and fix like above. Kerberos Armoring should also help here too.
Set GPO to NTLMv2 only, no v1 or LMHash (see pic)
11) Accounts vulnerable to AS-REP roasting
Get-ADuser -filter { DoesNotRequirePreAuth -eq "True" }
Ask why no Kerb preauth and fix like above. Kerberos Armoring should also help here too.
12) Weak password policy
CIS guidance of 60 days is too short
My recommendation (in order):
- Reject weak passwords (covered later)
- SSO all the things
- Increase length to around 16 characters, remove complexity, and push phrases/sentences
- 1 yr expiry
- Hashcat your users
CIS guidance of 60 days is too short
My recommendation (in order):
- Reject weak passwords (covered later)
- SSO all the things
- Increase length to around 16 characters, remove complexity, and push phrases/sentences
- 1 yr expiry
- Hashcat your users
13) Inactive accounts
Know your envinronment. I have thousands of accounts that go inactive depending on time of year or what the user signed up for.
Make flexible policies based on needs. This is 90 days:
Search-ADAccount –AccountInactive -TimeSpan 90.00:00:00 -UsersOnly
Know your envinronment. I have thousands of accounts that go inactive depending on time of year or what the user signed up for.
Make flexible policies based on needs. This is 90 days:
Search-ADAccount –AccountInactive -TimeSpan 90.00:00:00 -UsersOnly
14) Privileged accounts with old passwords
Use fine-grained password policies so privileged, interactive users have stricter requirements
Use gMSA or cred management solution to ensure service account passwords rotate often.
Create new accounts for new installs. Don't be lazy.
Use fine-grained password policies so privileged, interactive users have stricter requirements
Use gMSA or cred management solution to ensure service account passwords rotate often.
Create new accounts for new installs. Don't be lazy.
15) Users with weak passwords
I love Azure AD Password Protection:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-password-ban-bad-on-premises\\
But not everyone can afford it. @BHinfoSecurity is amazing and provides a free AD password filter that I'd be willing to trust putting in my AD.
https://www.blackhillsinfosec.com/the-creddefense-toolkit/
Education is key
I love Azure AD Password Protection:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-password-ban-bad-on-premises\\
But not everyone can afford it. @BHinfoSecurity is amazing and provides a free AD password filter that I'd be willing to trust putting in my AD.
https://www.blackhillsinfosec.com/the-creddefense-toolkit/
Education is key
16) Passwords in Group Policy Preferences
This has been blocked for a long time, but legacy GPO's still exist
Quick tool to find them:
https://github.com/l0ss/Grouper2
Consider new policies for each version of Windows (use WMI filters, add security baseline) to deprecate old policies.
This has been blocked for a long time, but legacy GPO's still exist
Quick tool to find them:
https://github.com/l0ss/Grouper2
Consider new policies for each version of Windows (use WMI filters, add security baseline) to deprecate old policies.
And for all that work, there's infinitely more to properly securing Active Directory.
Check out the content by the folks I've mentioned in the thread as that's a huge part of where I've learned what I know.
Last thing - be willing to ask questions. Smart people ask questions ;)
Check out the content by the folks I've mentioned in the thread as that's a huge part of where I've learned what I know.
Last thing - be willing to ask questions. Smart people ask questions ;)

 Read on Twitter
Read on Twitter